Quarter-end close is approaching. Advisors are trying to reconcile reports, operations staff are moving money, and leadership wants clean numbers without delay. Then the system slows down, a shared file sync fails, or an audit request lands with a hard deadline.
That is the point where weak IT stops being an inconvenience and becomes a business problem. For financial firms, technology touches the work that matters most: client data integrity, regulatory readiness, and uptime when timing is critical. Generic support desks may reset passwords and swap laptops. They do not reliably protect a finance firm’s operating model.
Strong it support for finance has a different job. It keeps books accurate, access controlled, evidence preserved, and critical systems available when teams need them most. That is not back-office plumbing. It is operational risk management.
Table of Contents
- Beyond Standard IT A New Reality for Financial Firms
- Why Generic IT Support Puts Your Firm at Risk
- Meeting Your Essential Security and Compliance Needs
- The Core Managed Services That Power Financial Firms
- Calculating the ROI of Specialized IT Support
- Your Checklist for Choosing the Right DFW IT Partner
- Take the First Step Toward Total IT Confidence
Beyond Standard IT A New Reality for Financial Firms
The familiar failure point is rarely dramatic at first. A report exports with mismatched fields. A portfolio file is locked at the wrong moment. A compliance manager asks for records and nobody is fully sure which system has the final version.
That is why financial firms outgrow standard IT faster than most industries. They are not just running office software. They are protecting records that drive decisions, audits, and client trust.

The stakes are operational, not technical
Finance firms handle sensitive information under pressure. A slowdown during closing, tax season, investor reporting, or a live transaction review can disrupt revenue and credibility at the same time.
Security pressure has also changed. Historical data shows a 650% increase in ransomware attacks on financial institutions from 2020 to 2023, and in the US the financial services industry faced 25% of all reported data breaches in 2024, with average losses of $5.9 million per incident according to Acceldata’s review of the critical role of data in finance.
A finance firm cannot treat those facts as somebody else’s problem. The target profile fits the industry too well: valuable data, high urgency, and expensive downtime.
A strategic IT partner changes the conversation
A specialized provider does more than wait for tickets. The right partner designs support around the firm’s business moments:
- During close periods: systems stay responsive, access is controlled, and core apps are monitored before bottlenecks become outages.
- During audits: records, logs, and permissions are easier to produce because evidence collection is built into daily operations.
- During security incidents: containment, recovery, and communication happen through a defined process rather than improvisation.
Financial firms do not need more generic troubleshooting. They need technology governance that supports the way finance work gets done.
That shift matters. Once leadership starts viewing IT as part of risk control and service delivery, investment decisions improve. Support becomes tied to continuity, compliance, and client confidence, which is exactly where it belongs.
Why Generic IT Support Puts Your Firm at Risk
Many firms still assume competent general IT is enough. It usually is not. Finance has too many edge cases, too much sensitive data, and too little tolerance for ambiguity.
A generic provider often treats a financial firm like any other office. That is the mistake.
Financial data is not ordinary business data
The financial sector depends on IT to manage large historical datasets. One clear example is the Jordà-Schularick-Taylor Macrohistory Database covering 17 economies since 1870, which shows the extent to which finance relies on structured long-range data management, as noted by the University of New Mexico finance history resource.
That same reality appears inside smaller firms in a practical way. Reports must tie out. Statements must stay consistent across systems. Historical records must remain accessible and defensible.
For a firm in Dallas-Fort Worth, IT support that ensures high data accuracy across statements is essential for preventing discrepancies that could lead to regulatory penalties under SOX or GDPR, with data consistency being a critical factor in compliance.
Generic IT teams often miss the business significance of a small mismatch. In finance, a synchronization error is not a nuisance. It can distort reporting, trigger rework, and create audit exposure.
Downtime hits finance firms differently
If a retailer loses access to a printer, business slows down. If a financial firm loses access to files, email archives, reporting systems, or secure remote access during a critical period, work can stop.
The issue is not just availability. It is timing. Financial firms run on deadlines that are externally enforced by clients, counterparties, and regulators. An outage during a calm week is bad. An outage during close is much worse.
A generic provider usually responds after users complain. A specialized provider designs for continuity before the pressure spike arrives.
Risk lives in the gaps between systems
Finance firms rarely rely on one platform. They operate with accounting packages, document systems, secure email, cloud storage, line-of-business applications, and sometimes older tools that nobody wants to touch before quarter-end.
That stack creates hidden failure points:
- Permission drift: people keep access they no longer need.
- Version confusion: teams work from different records and assume they are final.
- Application blind spots: one vendor supports the software, another supports the server, and no one owns the full workflow.
The most dangerous IT issue in a financial firm is often not a dramatic failure. It is the quiet inconsistency nobody notices until an audit, a client dispute, or a deadline exposes it.
Specialized it support for finance closes those gaps. That is the difference between fixing technology and protecting a firm’s actual business process.
Meeting Your Essential Security and Compliance Needs
Compliance in finance is not a side project. It is part of daily operations. If controls are weak, the problem does not stay inside IT. It reaches legal exposure, reputational damage, and executive accountability.
That is why security architecture and compliance architecture should be treated as the same conversation.
Start with access control and encryption
Regulatory compliance in finance demands IT frameworks with automated controls. Multi-factor authentication and data encryption cut unauthorized access risks by 99.9%, per NIST benchmarks, and non-compliance fines averaged $14.8 million in 2023, often caused by manual tracking errors that automated compliance software can prevent, according to Techlocity’s discussion of IT support for financial services.
Those numbers lead to a simple conclusion. Manual compliance processes are too fragile for a regulated financial environment.
A solid baseline includes:
- MFA on every meaningful access path. Email, cloud apps, VPN, admin accounts, and privileged systems should all require it.
- Encryption at rest and in transit. Sensitive records should not depend on user judgment for protection.
- Centralized identity management. Access should be reviewed, revoked, and documented from a single control plane when possible.
A finance firm that still relies on shared credentials, ad hoc exceptions, or informal approval chains is carrying unnecessary risk.
Build evidence collection into daily operations
Many firms prepare for audits as if audits are rare events. That approach wastes time and creates panic. The better model is continuous readiness.
That means the environment should produce evidence as a normal byproduct of work:
- login history
- privileged access records
- device health status
- patching records
- backup verification
- policy acknowledgments
- exception tracking
When those records are fragmented across inboxes, spreadsheets, and screenshots, audit preparation becomes expensive and unreliable. When they are centralized through tools such as SIEM, identity platforms, and compliance workflows, audit response becomes faster and cleaner.
Translate regulations into operating controls
The specific legal framework varies by firm, but the technology implications are usually clear. GLBA pushes firms toward stronger safeguards for customer information. SOX increases the importance of integrity, control, and documentation around systems that affect reporting. PCI-DSS adds strict expectations where payment data is involved.
A practical leadership review should ask:
| Requirement area | Operating question | What strong IT support does |
|---|---|---|
| Access | Who can reach sensitive systems and why | Enforces MFA, role-based access, and review workflows |
| Data protection | How is client and financial data secured | Applies encryption, endpoint controls, and secure transfer methods |
| Auditability | Can the firm prove what happened | Preserves logs, alerts, and change records |
| Recovery | Can the firm restore operations cleanly | Tests backup and recovery processes before a crisis |
A compliant environment is not the one with the thickest policy binder. It is the one that can prove controls are active, enforced, and repeatable.
Finance leaders should expect IT support to reduce compliance effort, not add to it. If the current provider cannot explain how controls map to audit readiness, the provider is not aligned with the firm’s obligations.
The Core Managed Services That Power Financial Firms
Managed services only matter if they support business outcomes. For financial firms, the outcomes are clear: stable operations, protected records, rapid recovery, and less audit friction.
That makes the service stack easier to evaluate. Each service should solve a known business risk.
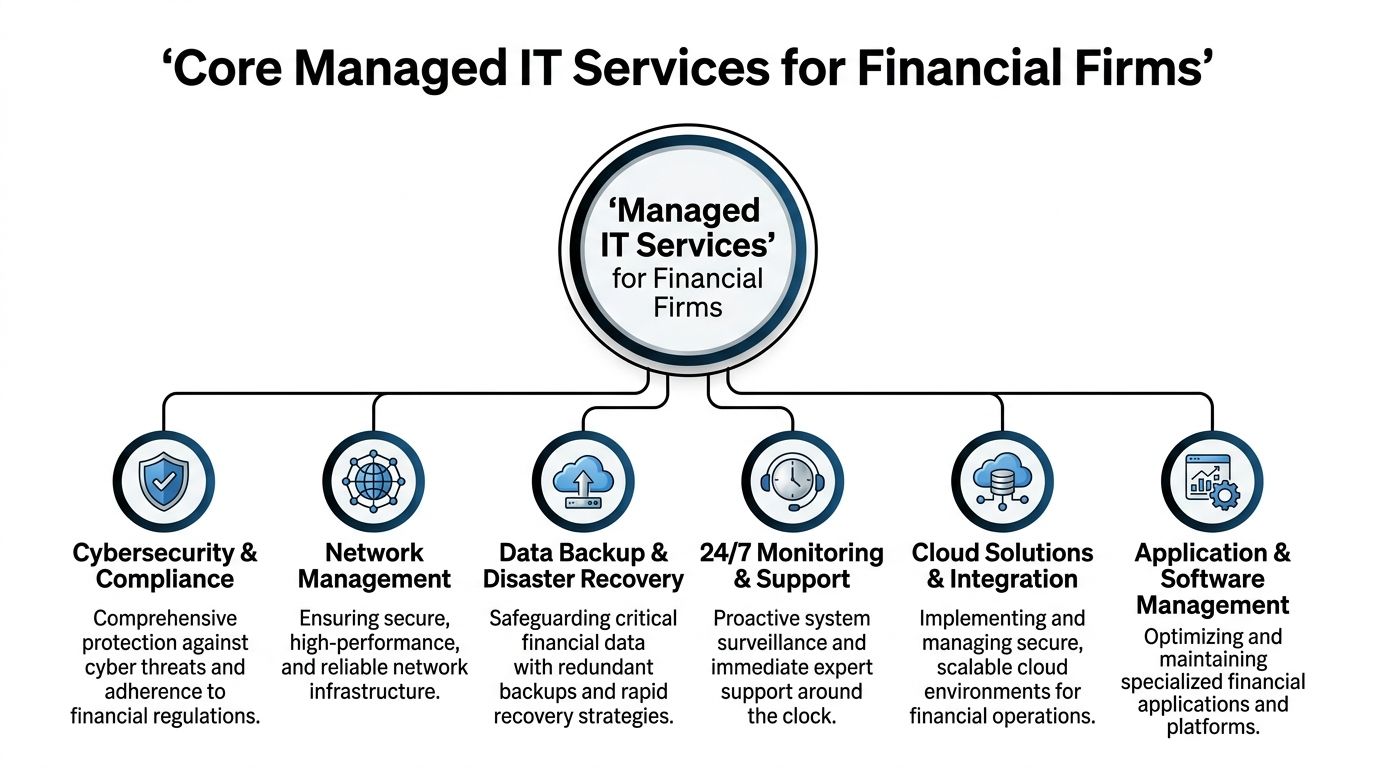
Proactive monitoring protects revenue hours
Proactive IT monitoring and managed services reduce downtime by up to 80% compared to reactive models. For financial firms, where breach costs average $5.9 million, proactive services that ensure 99.99% uptime and resolve issues in under an hour are critical for revenue loss prevention, according to Synergy Technical’s analysis of managed IT for financial services.
That matters most during the moments when the firm cannot afford delay. Monitoring should cover servers, cloud platforms, endpoints, line-of-business applications, storage health, and suspicious login behavior. The goal is not more alerts. The goal is intervention before a user notices failure.
Backup and disaster recovery protect the firm’s memory
A financial firm’s value is tied to its records. Client files, reporting data, communication history, workpapers, and system configurations all matter.
Strong backup strategy should include several layers:
- Immutable backup copies: records cannot be altered by an attacker or accidental deletion.
- Cloud backup with verification: data is not just stored. It is checked.
- Recovery planning tied to business priorities: the close system, client records, and identity services should come back first.
Too many firms assume backup is handled because a vendor once enabled it. That is not a strategy. Recovery has to be tested against real business scenarios.
Endpoint protection and secure access reduce exposure
Most incidents start at the edge. A laptop, a mailbox, a remote login, or a third-party integration creates the opening.
The right managed environment typically combines tools and controls such as:
- Endpoint detection and response
- Managed patching
- MFA-backed remote access
- Email security
- Device policy enforcement
- Encryption across laptops and mobile workflows
This matters even more for hybrid teams. Finance staff work from home, branch offices, and client sites. Secure access cannot depend on office walls anymore.
Cloud and application management keep teams productive
Financial firms increasingly depend on cloud suites, document systems, and specialized applications. Those tools need governance, not just licensing.
The most effective support model focuses on how platforms interact:
| Managed service | Business problem it solves | Finance impact |
|---|---|---|
| 24/7 monitoring | Issues are discovered too late | Reduces disruption during reporting and transaction windows |
| Backup and disaster recovery | Data loss or ransomware recovery stalls work | Preserves records and restores operations faster |
| Endpoint and identity security | Unauthorized access and malware exposure | Protects client data and reduces incident risk |
| Cloud and app management | Tools drift, break, or create workflow friction | Keeps teams efficient and improves consistency |
| Compliance-focused reporting | Audit requests trigger manual scrambling | Makes evidence easier to produce |
The best managed services program does not feel like a pile of tools. It feels like a controlled operating environment.
That is the standard finance firms should demand. If the current provider only talks about tickets closed, they are measuring the wrong thing.
Calculating the ROI of Specialized IT Support
A finance firm should not evaluate IT support as a monthly line item in isolation. The correct comparison is between the cost of structured support and the cost of operational instability.
The wrong comparison hides the true cost. Leadership teams often compare managed IT pricing to the salary of one internal technician or the lower bid from a general provider. That is incomplete. The true comparison includes downtime, recovery effort, delayed billing, partner distraction, audit friction, and client confidence.
A firm that wants a stronger framework for this conversation can review managed IT revenue and efficiency considerations in financial services.
The important question is not whether specialized support costs more than minimal support. The question is whether the current model leaves expensive risks unaddressed.
ROI in finance comes from avoided disruption
Specialized it support for finance produces value in a few predictable ways.
First, it reduces the number of business interruptions that consume high-value staff time. Partners, controllers, and operations leaders should not spend prime hours chasing file access issues or unclear system ownership.
Second, it shortens the duration of incidents that do occur. That protects deadlines and reduces the internal cost of rework.
Third, it improves consistency. Standardized device management, access control, backup verification, and documentation reduce the hidden drag that accumulates across every reporting cycle.
A better way to evaluate the investment
A practical review should ask these questions:
- How many partner or manager hours are lost each month to preventable IT friction?
- What happens to billing, close timelines, or client service when a core system is unavailable?
- How much staff effort goes into preparing documentation that should already exist?
- How exposed is the firm if one key employee or one vendor relationship disappears?
This approach is more honest than asking whether support can be purchased a little cheaper. Cheap support often pushes cost into other departments where it becomes harder to track.
The strongest ROI case for specialized IT is not flashy technology. It is steady operations, cleaner audits, and fewer expensive surprises.
For financial firms, that is a serious return.
Your Checklist for Choosing the Right DFW IT Partner
Selecting an IT partner for a financial firm should feel more like vendor due diligence than a casual service purchase. Marketing language is easy. Evidence is harder.
The right evaluation process should test whether a provider understands finance-specific risk, not just general infrastructure.
What to ask before signing anything
A useful starting point is strategic oversight. If a provider cannot discuss roadmap, risk posture, and leadership planning, the relationship will stay reactive. Firms that need that higher-level guidance should look closely at options such as a virtual CIO service for IT strategy and governance.
Then the questions should become more specific.
| Evaluation Area | Key Question to Ask | Why It Matters |
|---|---|---|
| Finance industry fit | Which financial or accounting environments has the provider supported | Experience shapes how the provider handles audits, deadlines, and data sensitivity |
| Compliance readiness | How does the provider map controls to GLBA, SOX, PCI-DSS, or related obligations | The firm needs operating controls, not vague promises |
| Monitoring and response | What gets monitored, who responds, and how are escalations handled | Response quality determines whether small issues become business disruptions |
| Backup and recovery | How are backups verified and how is recovery tested | Backup without proof of recoverability is a false comfort |
| Identity and access | How are MFA, user provisioning, and offboarding managed | Access control failures create direct business and compliance risk |
| Documentation | What reports, logs, and review records are provided to leadership | Good documentation lowers audit pain and improves accountability |
| Local presence | When on-site help is needed in DFW, how does the provider handle it | Local support still matters when hardware fails or urgent coordination is required |
Red flags that deserve immediate scrutiny
Some warning signs are easy to miss during sales calls.
- Tool-first answers: the provider lists products but cannot explain the business risk each one addresses.
- Weak ownership: application issues get pushed back to software vendors with no clear coordination plan.
- No governance rhythm: there are no scheduled reviews of risk, performance, or lifecycle planning.
- Generic compliance language: the provider says it “takes security seriously” but cannot describe evidence, controls, or escalation paths.
Why local context still matters
A DFW-based firm often benefits from a partner that understands the local operating environment, can arrive on site when necessary, and is positioned to build working relationships with leadership rather than just process tickets from afar.
That does not replace strong remote capabilities. It complements them. Finance firms need both.
A strong IT partner speaks in business terms. They should be able to explain how support decisions affect close timelines, audit readiness, and client trust.
If a provider cannot do that in the sales process, they will not do it well during a crisis.
Take the First Step Toward Total IT Confidence
Financial firms do not need more complexity. They need clarity.
The path forward is straightforward. Protect the integrity of client and financial data. Strengthen access controls. Build audit evidence into daily operations. Put monitoring and recovery around the systems that the business cannot afford to lose. Then review the environment regularly with leadership, not just when something breaks.
That is what effective it support for finance looks like. It aligns technology with the firm’s actual obligations and pressure points. It supports service delivery, reduces operational drag, and gives leadership a cleaner view of risk.
Waiting for a failed audit, a ransomware event, or a quarter-end outage is the expensive route. A focused assessment now is the better move. It reveals the gaps, prioritizes fixes, and gives the firm a practical roadmap instead of assumptions.
For many DFW firms, the first useful step is not a full overhaul. It is an objective health check. Leadership needs to know which controls are solid, which workflows are fragile, and where support is too generic for the firm’s risk profile.
Technovation LLC helps DFW financial firms turn IT into a controlled, audit-ready business function instead of a recurring source of uncertainty. Firms that want a clearer picture of their current risk posture can start with a conversation and a practical assessment through Technovation LLC.