Is the business secure, or has it been lucky so far?
That question matters because most SMBs do not fail on cybersecurity because they ignored technology. They fail because they mistook a few tools for a strategy. Antivirus is not a strategy. A firewall is not a strategy. A cyber policy with no monitoring, no testing, and no compliance roadmap is paperwork.
For Dallas-Fort Worth businesses in healthcare, legal, finance, construction, and nonprofits, the gap is even wider. Generic national advice often focuses on broad basics. It seldom answers the core question regulated firms face: which cybersecurity solutions for business reduce risk, support compliance, and protect uptime without burying a small team in complexity?
The right answer is not “buy more software.” The right answer is to build a security plan around business operations, regulatory obligations, and recovery speed.
Table of Contents
- Why Your Business Needs a Cybersecurity Strategy in 2026
- Understanding the Pillars of Modern Cybersecurity
- How to Prioritize Cybersecurity Investments
- Your Cybersecurity Implementation Roadmap
- Calculating the Cost and ROI of Cybersecurity
- A Checklist for Choosing the Right Cybersecurity Partner
- Take the First Step Toward Proactive Protection
Why Your Business Needs a Cybersecurity Strategy in 2026

A business without a cybersecurity strategy is making an expensive bet. It is betting that attackers will not notice weak access controls, untested backups, outdated endpoints, or unmanaged vendor connections.
That bet is getting worse. 57% of SMBs now rank cybersecurity as their top business priority, up from 43% the previous year according to ConnectWise SMB cybersecurity statistics and trends. The same source reports that micro-businesses see successful breaches in 43% of attacks, with average losses of $120,000, and 60% close within six months after a breach.
Those numbers matter, but the business point is simpler. Security is no longer an IT side task. It protects revenue, client trust, insurance posture, and operational continuity.
Security is a business control, not just a technical tool
A strong cybersecurity plan works like a silent alarm system. Most of the value comes from what never happens. No ransomware event that locks scheduling. No email compromise that redirects payment. No compliance miss that turns a security incident into a regulatory problem.
For regulated firms, that shift is critical.
A medical clinic has to protect patient data and keep systems available. A law firm has to control document access and preserve client confidentiality. A financial firm has to reduce exposure across identities, devices, cloud tools, and vendor connections. In each case, the question is the same: what failure would stop the business from operating normally?
Key takeaway: The practical purpose of cybersecurity solutions for business is not to “win against hackers.” It is to keep operations running, keep sensitive data controlled, and keep the business out of preventable compliance trouble.
No visible problem does not mean low risk
Many owners assume security is fine because nothing dramatic has happened yet. That is weak logic. Most damaging incidents start subtly. A compromised account may sit unnoticed. A cloud permission mistake may expose data long before anyone reviews it. A vendor weakness may create the opening.
That is why 2026 planning should focus less on buying isolated tools and more on building a managed system. The businesses that hold up under pressure are the ones that know what matters most, watch it continuously, and rehearse recovery before they need to.
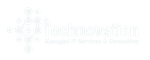
Understanding the Pillars of Modern Cybersecurity
A complete security posture is layered. The easiest way to explain it is a castle model. Walls slow attackers down. Lookouts spot unusual movement. Defenders contain damage if someone gets inside. Modern cybersecurity solutions for business work the same way.
Prevention stops obvious threats
Prevention is the outer wall. It includes identity controls, network rules, secure remote access, endpoint protection, and user training.
The job here is simple. Make common attacks harder to launch and harder to spread.
Some controls live at the user level:
- Identity and access management limits who can reach systems and data.
- Role-based permissions reduce unnecessary exposure.
- Security awareness training lowers the odds that staff approve the wrong login prompt or trust the wrong message.
Others sit in the environment:
- Firewalls and secure VPN access shape how traffic enters and leaves.
- Cloud security controls lock down storage, admin privileges, and shared resources.
- Endpoint protection watches laptops, servers, and mobile devices where many attacks begin.
Detection catches what prevention misses
No defensive layer is perfect. Detection exists because attackers do not always behave like known malware. Modern endpoint tools are important in these situations. VMware Carbon Black Cloud uses behavioral analytics to stop threats that traditional antivirus misses, including ransomware encryption patterns in real time, and achieved 99.9% efficacy in MITRE ATT&CK evaluations according to IPKeys on cybersecurity tools.
That matters in plain business terms. Signature-based antivirus looks for known bad files. Behavioral tools look for suspicious actions. If a device starts modifying files in a pattern consistent with ransomware, a capable endpoint platform can flag or block it before the incident spreads.
A practical distinction looks like this:
| Security layer | What it watches | Business outcome |
|---|---|---|
| Traditional antivirus | Known malware signatures | Basic malware filtering |
| Behavioral endpoint protection | Suspicious actions and anomalies | Faster disruption of unknown or evolving attacks |
| Monitoring and alerting | Activity across systems and users | Earlier investigation and containment |
Response and recovery keep the business operating
The final pillar is response. Many SMBs are weakest in this area.
Response includes incident handling, backup recovery, isolation steps, escalation paths, and documentation. If prevention is the wall and detection is the lookout, response is the team that closes the gate, contains the breach, and gets operations moving again.
That means:
- Documented incident response so staff know who acts first.
- Reliable backups that are tested, not assumed.
- Recovery priorities based on critical workflows, not just servers.
- Compliance-aware evidence handling when regulated data is involved.
Tip: A security stack without a response process is incomplete. Tools can create alerts. Only a real operating plan restores the business.
How to Prioritize Cybersecurity Investments
Most SMBs cannot fund everything at once. That is fine. The mistake is spending evenly across low-impact tools while ignoring the systems, data, and compliance gaps that would cause the most damage.
The smartest path is risk-first. For a DFW regulated business, that usually means protecting the data that creates legal exposure and the systems that create operational dependency.
Start with regulated data and operational choke points
Generic bundles often fail regulated firms because they are built for broad coverage, not audit pressure. Regulated sectors in Texas face 25% higher breach costs due to non-compliance fines, and tailoring defenses to standards like HIPAA or GLBA through a local MSP can reduce exposure by 40-60% and deliver 2.5x better ROI than a DIY approach according to Cynet on cybersecurity for small businesses.
That changes the investment order.
A healthcare practice should not start by shopping for miscellaneous tools. It should start by identifying where protected health information lives, who can access it, how it is backed up, and what systems must stay online for patient care and scheduling.
A law firm should focus first on document access controls, endpoint visibility, email security, and response procedures around confidential client data.
A financial or accounting firm should prioritize identity protections, privileged access, logging, endpoint controls, and cloud configuration review around systems tied to financial records and client portals.
A practical order of operations
A pragmatic sequence often looks like this:
- First, map critical assets. Identify regulated data, line-of-business apps, admin accounts, remote access points, and key vendors.
- Second, fix high-consequence gaps. Weak permissions, unmanaged devices, stale accounts, and untested backups deserve attention before nice-to-have tools.
- Third, align controls to compliance. HIPAA, GLBA, and client confidentiality expectations should shape logging, access review, retention, and response workflows.
- Fourth, build repeatable oversight. Monitoring, review cadence, and documented ownership matter more than a long list of unused products.
For businesses evaluating providers, one option is Technovation LLC, a DFW managed service provider that offers cybersecurity, compliance support, 24/7 monitoring, cloud backup, risk mitigation, and free security audits for regulated and security-conscious organizations.
Decision rule: Fund the controls that protect the most sensitive data and the most fragile business processes first. Everything else comes after that.
Your Cybersecurity Implementation Roadmap
Buying software is easy. Running a secure environment is the hard part. Effective cybersecurity solutions for business need a rollout plan, operating discipline, and continuous review.
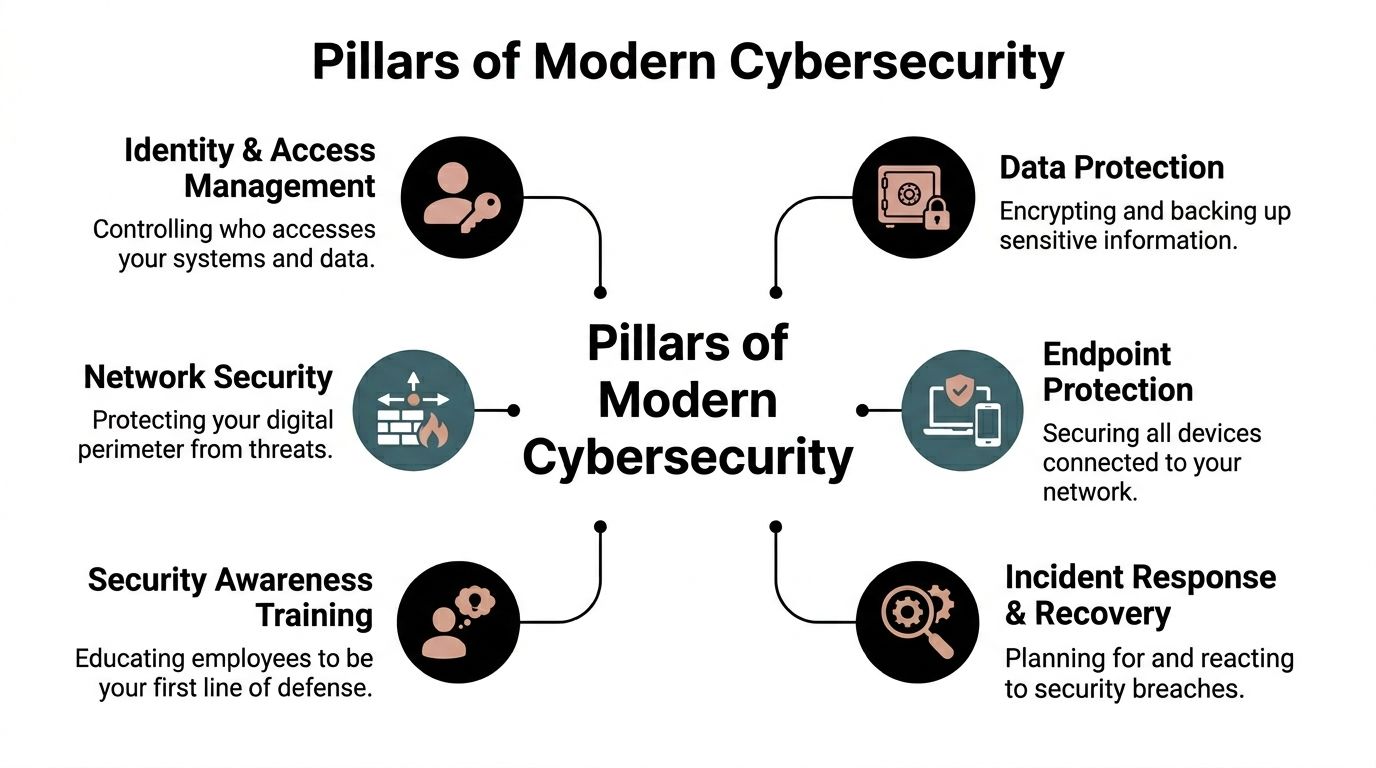
Phase one assessment
The first phase is an assessment. Not a vague conversation. A real inventory and risk review.
That means identifying:
- Critical systems such as EHR platforms, accounting tools, document systems, and remote access services
- Sensitive data locations across endpoints, servers, cloud storage, and line-of-business apps
- Access paths including admin accounts, third-party logins, and vendor connections
- Compliance obligations tied to healthcare, legal, finance, or contractual requirements
This is also where the business decides what must recover first. If scheduling, billing, or document access goes down, leadership should already know the order of restoration.
Phase two deployment and configuration
The second phase is implementation. During this phase, many teams move too fast and create blind spots.
Good deployment is controlled. Endpoint protection gets tuned, not just installed. Policies get matched to user roles. Backup jobs get configured around actual recovery priorities. Remote access gets hardened. Logging gets enabled where it can support both security review and compliance evidence.
For teams reviewing authentication as part of this phase, this small business guide to implementing multi-factor authentication is a useful practical reference.
A co-managed approach works well here because internal staff already know business workflows, while outside specialists can harden the environment without forcing an unrealistic all-at-once change.
Phase three ongoing management
This phase matters most because attackers do not care when a project ended. Environments change. Staff changes. Vendors change. Cloud permissions drift. New devices appear. Old accounts stay active unless someone removes them.
For construction and engineering firms, this is especially important because 60% of SMB breaches stem from third-party or supply chain vulnerabilities, AI-driven tools can cut these threats by 50%, 72% of SMBs lack them, and a co-managed model combining network hardening with 24/7 monitoring can prevent 80% of related downtime according to the SBA cybersecurity guidance referenced in the verified data.
A workable management cadence includes:
- Continuous monitoring for endpoints, identities, and suspicious behavior
- Backup testing so recovery capability is proven
- Access review for user roles, admin rights, and vendor accounts
- Incident plan updates after system or staffing changes
- Periodic compliance checks tied to actual operational workflows
Practical advice: Set-and-forget security is not security. It is deferred cleanup.
Calculating the Cost and ROI of Cybersecurity
Most owners do not need a lecture on cyber risk. They need a business case. That case should compare predictable prevention spend against unpredictable interruption, recovery work, compliance fallout, and lost trust.
The cost side is predictable
A managed security program usually shows up as a planned operating expense. Such programs are useful. Planned costs are easier to budget than emergency response, lost billable time, legal review, client notification, and reputation repair after an avoidable incident.
Leadership should stop asking, “What does security cost?” and start asking, “What business interruption is being bought down?”
A proper model should include:
- Downtime exposure tied to systems the business cannot run without
- Recovery effort for rebuilding devices, accounts, and access
- Compliance work after an incident involving regulated or confidential data
- Leadership time diverted away from growth and operations
The return comes from avoided disruption
The clearest return on cybersecurity is preserved continuity. If a business avoids a multi-day outage, a preventable account compromise, or a compliance-triggered mess, the return is real even if it never appears as a line item called “profit from security.”
For planning, leadership teams benefit from strategic guidance rather than product shopping. A virtual CIO service can help map security spending to business priorities, compliance obligations, and staged implementation.
The financial logic is straightforward:
- Prevention costs are usually known in advance
- Incident costs are often clustered, urgent, and disruptive
- Stronger controls support insurability, client confidence, and audit readiness
- Better planning reduces waste on tools that do not address core risk
The best ROI conversations stay grounded in operations. If the control does not protect uptime, sensitive data, contractual obligations, or audit readiness, it may not deserve early budget.
A Checklist for Choosing the Right Cybersecurity Partner
Many SMBs already pay an IT provider. That does not mean they have a real security partner.
This distinction matters because 58% of SMBs see enhanced security as a key MSP benefit, yet 73% doubt their provider can fully protect them, and 47% would switch for better protection according to Pontual Solutions on 2025 cybersecurity trends for businesses. Trust is not won by promising everything. It is earned through clear scope, accountability, and operational discipline.
Questions that expose weak providers
A serious provider should answer plain questions without hiding behind jargon.
Use this checklist:
- What is monitored continuously? If the answer is vague, the service is probably reactive.
- How are compliance needs handled for healthcare, legal, or finance? A provider that treats every client the same will miss industry-specific risk.
- What happens during an incident? Ask who is contacted, how systems are isolated, and how evidence is handled.
- How are backups tested? A backup that has never been restored is an assumption.
- How are third-party and remote access risks reviewed? Vendor connections are part of the attack surface.
- Who owns strategy? Tool management matters, but leadership also needs roadmaps, priorities, and decision support.
What a strong fit looks like in DFW
A strong cybersecurity partner should look like an extension of the business, not a ticket queue.
That often means:
- Local responsiveness for firms that need fast help in the DFW area
- Regulated industry familiarity with HIPAA, GLBA, client confidentiality expectations, and audit pressure
- Co-managed flexibility for internal IT teams that need support rather than replacement
- Operational focus on uptime, recovery, and documented process
- Clear reporting that leadership can use
A good partner does not just install tools. A good partner helps leadership make better risk decisions.
The wrong provider sells products. The right one helps the business decide what must be protected first, how to prove controls are working, and how to recover without chaos.
Take the First Step Toward Proactive Protection
Cybersecurity gets easier to manage once the business stops treating it like a shopping list.
The winning approach is narrower and more disciplined. Identify the systems that keep the company operating. Protect the data that creates compliance and reputation risk. Build layered controls around access, endpoints, backups, monitoring, and response. Then keep the whole program under review.
That is the gap many DFW businesses still need to close. National advice tends to stay generic. Regulated local firms need security tied to actual operations, real audit demands, and the limits of a small or midsized team.
A medical office does not need ten disconnected tools. It needs controlled access, dependable recovery, and documentation that stands up under scrutiny. A law firm needs confidentiality preserved across devices, email, and files. A financial firm needs tighter identity control and stronger operational oversight. A construction company needs vendor risk and remote access handled with discipline.
The right next step is not another rushed software purchase. It is an assessment that shows where the business is exposed, which gaps matter most, and what order to fix them in.
A DFW business that wants a clearer security roadmap can start with a complimentary, no-obligation security audit from Technovation LLC. That gives leadership a concrete view of current risk, compliance gaps, recovery priorities, and the cybersecurity solutions for business that deserve attention first.