Most DFW businesses don't have a compliance problem. They have an execution problem.
The rules usually aren't the mystery. The main issue is knowing which data matters, where it lives, who can touch it, and whether the business can prove its controls work when an auditor, client, insurer, or regulator asks. That's where data security and compliance stops being a legal checklist and becomes a business decision.
For a clinic, law firm, accounting practice, or engineering company, weak execution creates avoidable risk. It also creates missed opportunity. Buyers trust firms that can answer security questions cleanly. Partners move faster with vendors that already have documentation, policies, and evidence in order. Insurance conversations go better when leadership can show discipline instead of improvisation.
Table of Contents
- Beyond the Buzzwords of Data Security and Compliance
- Understanding Data Security vs Data Compliance
- Navigating Key Regulations in Your Industry
- Building Your Defense with Practical Controls
- A Step-by-Step Roadmap to Compliance Readiness
- Common and Costly Compliance Mistakes to Avoid
- How Technovation Builds Your Compliance Foundation
Beyond the Buzzwords of Data Security and Compliance

Compliance is a business asset
A lot of owners still treat compliance like rent. Necessary, annoying, and disconnected from growth. That's the wrong frame.
A stronger frame is this. Compliance is proof that the business runs with control. Data security is how that control gets enforced. When a prospect asks how client files are protected, when a bank requests documentation, or when cyber insurance underwriting gets tougher, disciplined companies answer faster and with less internal chaos.
The financial risk is no longer abstract. In 2025, the average cost of a data breach in the United States reached $10.22 million, which shows how directly compliance gaps tie to financial exposure, according to 2025 breach cost reporting.
Practical rule: If leadership can't quickly show where sensitive data lives, who has access, and how incidents are handled, the business isn't managing risk. It's hoping.
For DFW firms, this matters beyond penalties. Healthcare groups depend on patient trust. Law firms depend on confidentiality. Financial firms depend on control, recordkeeping, and clean process. In each case, weak data security and compliance creates friction that spills into operations, contracts, and reputation.
Trust is easier to keep than rebuild
Most owners don't need more fear. They need a better operating model.
Strong compliance posture makes routine business easier. Vendor reviews take less time. Mergers and partnerships involve fewer surprises. Employee turnover is less dangerous because access and documentation are already structured. Even internal decision-making improves when leadership knows which systems hold regulated or confidential data.
That shift matters in a crowded local market. Plenty of firms claim they take security seriously. Fewer can demonstrate it with documented controls, tested response plans, and a current inventory of sensitive data. Buyers notice the difference.
The point isn't to build bureaucracy. It's to build reliability. Reliable businesses win better clients, recover faster from problems, and spend less time cleaning up preventable mistakes.
Understanding Data Security vs Data Compliance

Security builds the house
Business owners often blend these terms together. They shouldn't.
Data security is the protection layer. It includes access restrictions, encryption, monitoring, backups, endpoint protection, incident response, and the policies that govern how data gets handled. In plain language, security is the house itself. Doors lock. Windows shut. Alarms work. The wiring isn't exposed.
If a law office stores client records in a cloud platform, security decides who can log in, whether files are encrypted, whether unusual activity gets flagged, and whether a former employee loses access immediately after departure. Those are operational controls, not legal opinions.
Security is also ongoing. A secure environment doesn't stay secure because someone bought software once. Staff roles change. Systems expand. Cloud storage multiplies. Remote access becomes normal. Every one of those changes can gradually weaken controls if no one is paying attention.
Compliance passes the inspection
Data compliance is the proof layer. It confirms the business meets the rules that apply to its industry, contracts, clients, and geography. Using the same analogy, compliance is the building inspection. It asks whether the house meets code, whether required safeguards exist, and whether the owner can document them.
A healthcare practice may have encryption and user controls in place, but if it can't show policy documentation, breach processes, and workforce training, it may still have a compliance problem. A financial firm may have decent security tools, but if records are retained inconsistently or reviews aren't documented, the inspection can still fail.
Good security without compliance proof creates audit pain. Compliance paperwork without real security creates false confidence.
The strongest businesses treat these as linked but separate disciplines:
- Security reduces the chance of harm: It lowers the odds of unauthorized access, data loss, or prolonged disruption.
- Compliance proves accountability: It shows customers, auditors, insurers, and regulators that controls aren't just promised. They're defined, assigned, and maintained.
- Both require process: A business can't improvise either one under pressure and expect a clean outcome.
The house analogy matters because many companies overinvest in one side. Some buy controls and ignore documentation. Others draft policies and skip technical enforcement. Both approaches fail in practice.
For DFW businesses in regulated sectors, the standard should be simple. Build a secure house. Keep records that prove it passes inspection. Repeat that discipline every time the business changes.
Navigating Key Regulations in Your Industry
Different industries don't face the same compliance pressure. A family medical clinic, a regional CPA firm, and a design firm bidding on government-related work won't answer the same questions or protect the same categories of information. That's why generic advice usually wastes time.
DFW industry compliance cheat sheet
| Industry | Key Regulations | What It Primarily Protects |
|---|---|---|
| Healthcare clinics and medical practices | HIPAA and related patient privacy obligations | Protected health information, patient records, treatment data, billing data |
| Financial services and accounting firms | GLBA, SOX, PCI DSS, client contractual security requirements | Financial records, customer financial information, payment card data, audit trails |
| Law firms and legal service providers | State privacy obligations, client confidentiality duties, contractual security terms | Client files, case documents, communications, personally sensitive records |
| Construction, engineering, and architecture firms serving regulated clients or government contracts | CMMC, contract-driven cybersecurity requirements, controlled project data safeguards | Controlled unclassified information, project documents, contracts, technical data |
| General SMBs and nonprofits | State privacy duties, breach notification obligations, insurer and customer security requirements | Employee records, donor data, customer information, business operations data |
That table isn't a substitute for legal advice. It is a practical filter. If leadership can't point to the data category that matters most, the business is already behind.
What business owners usually miss
Most firms focus on the name of the regulation and miss the operational burden underneath it. Regulations don't just require secure technology. They require repeatable business behavior.
Three issues show up constantly:
- Scope confusion: Teams protect the main server and ignore file shares, old cloud folders, personal inboxes, and archived data.
- Documentation gaps: Controls may exist, but no one can produce policies, review logs, access decisions, or training records cleanly.
- Vendor spillover: A business may follow internal rules but still expose itself through billing partners, outside counsel, consultants, or software providers.
A DFW law firm, for example, might think confidentiality is enough. It isn't. The firm also needs controlled access, documented retention practices, secure remote work, and a clear response process if sensitive files are exposed.
A healthcare practice often has the opposite problem. It knows the rulebook but operates with patchwork systems and inconsistent staff habits. That creates a gap between intention and evidence.
The right question isn't, "Which regulation applies?" The better question is, "What proof would the business struggle to produce tomorrow?"
That answer usually points straight to the first real compliance project.
Building Your Defense with Practical Controls
A compliance program gets real when it moves from policies on paper to controls that shape daily work. That means fewer broad promises and more enforceable rules.
Start with access and data protection
A practical framework helps. The NIST SP 800-53 framework includes over 1,000 security and privacy controls, and one control family alone, Access Control, can reduce unauthorized access risk by up to 70% in audited environments. That matters because unauthorized access accounts for 80% of breaches, according to NIST-aligned control guidance.
The lesson isn't that every SMB needs a giant federal-style program. It's that smart control design works. Businesses should start with the controls that shape exposure most directly:
- Access controls: Limit data access by role, not convenience. If staff can see everything, the business has already failed least privilege.
- Encryption: Protect data at rest and in transit so exposed systems don't automatically become exposed records.
- Logging and monitoring: Record meaningful activity and review it. Silent environments give attackers and internal mistakes too much time.
- Backups and recovery discipline: Recovery isn't just about having copies. It depends on whether the business can restore critical data cleanly and quickly.
A DFW accounting firm doesn't need every safeguard at once. It does need a deliberate starting point, especially around user access, remote work, and sensitive document handling.
Turn controls into operating discipline
Controls fail when they live in isolation. The firewall team doesn't talk to leadership. HR changes a role, but IT doesn't update permissions. A vendor gets onboarded without risk review. That's how businesses end up technically equipped but operationally exposed.
A stronger model ties controls to ownership and review:
- Assign control owners: Someone must own user reviews, vendor checks, backups, and incident handling.
- Define evidence: Each control needs proof. Logs, screenshots, approvals, review records, and policy documents all count.
- Review on a schedule: Security discipline fades when reviews happen only after a scare.
- Align controls to the business: A clinic, law office, and finance firm won't prioritize the same workflows.
For businesses that need help turning these controls into a managed operating system, business cybersecurity solutions in DFW can support the technical and procedural side together.
Controls should make bad decisions harder, not just document that they were discouraged.
That standard keeps data security and compliance grounded in business reality instead of theory.
A Step-by-Step Roadmap to Compliance Readiness
Most businesses don't fail because they don't care. They fail because compliance gets treated like a side project with no sequence, no ownership, and no operating rhythm.
Why most programs stall
That pattern shows up clearly in the numbers. While 91% of companies plan to implement continuous compliance, 41% lack the tools to enforce policies and 47% say their technical privacy teams are understaffed, according to compliance readiness reporting. Ambition isn't the issue. Execution is.
That gap is especially familiar in small and midsized firms across DFW. Leadership delegates compliance to IT, operations, HR, or an office manager, but no one has full visibility or enough time. The result is partial progress, stale documentation, and unresolved risk.
The six-step roadmap that works
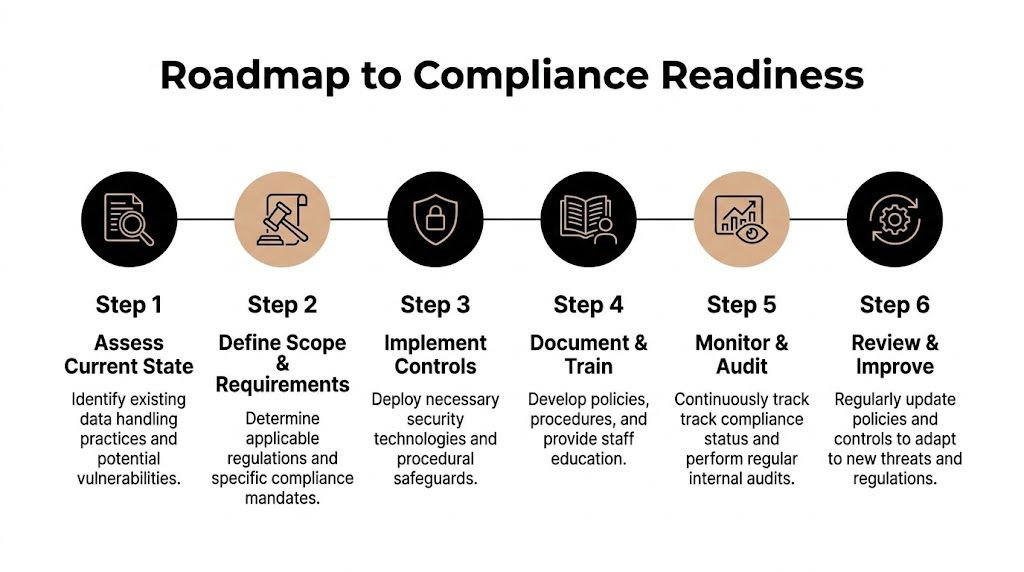
A workable roadmap is straightforward when the business follows it in order.
Assess current state
Start with the truth, not assumptions. Review how the business stores, shares, backs up, and deletes sensitive data. Include cloud apps, employee devices, shared folders, and third-party access.Define scope and requirements
Identify which obligations apply to the business. Industry rules matter, but so do client contracts, insurance requirements, and data-sharing commitments. Scope keeps teams from solving the wrong problem.Implement controls
Put technical and administrative safeguards in place. Focus first on high-risk areas such as access rights, encryption, backup integrity, incident handling, and vendor oversight.
A compliance program gets traction when leadership can name the next control to implement, the owner responsible for it, and the evidence that will prove it's working.
Document and train
Policies can't stay trapped in a shared drive. Staff need to know what the rules are, when exceptions require approval, and how to respond when something looks wrong. Training also exposes process gaps that technology alone won't fix.Monitor and audit
Review logs, test controls, confirm access rights, and check whether documented procedures match real-world behavior. Internal audits don't need to be theatrical. They need to be honest.Review and improve
Businesses change constantly. New hires, new software, new clients, and new AI workflows all change risk. Compliance readiness depends on regular adjustment, not a one-time sprint.
This roadmap works because it respects how SMBs operate. It creates sequence, accountability, and momentum. That is what most organizations are missing.
Common and Costly Compliance Mistakes to Avoid
Most compliance mistakes aren't dramatic. They're ordinary decisions repeated long enough to become expensive.
The blind spots that keep showing up
The first mistake is treating compliance like a finish line. A business passes an assessment, updates a policy binder, and assumes the hard part is over. Then the company adds a new cloud app, hires remote staff, changes vendors, or expands into a new service line. The environment changes, but the controls don't.
The second mistake is ignoring third-party exposure. Many firms tighten internal access and still hand sensitive information to outside providers without clear review, documentation, or ongoing oversight. That isn't delegation. It's outsourced risk.
Another common error is incomplete data mapping. Teams know where primary records sit, but not the copies, exports, shared folders, archived files, and duplicate datasets spread across different systems. That makes response, retention, and audit evidence far harder than it should be.
AI made one old problem much worse
AI didn't create poor data governance. It exposed it.
As AI use expands, 79% of organizations can't classify the sensitive data feeding their AI systems, and 77% fail to enforce proper access rights, according to AI data visibility findings. For SMBs, that's a serious compliance issue because sensitive information can move into new workflows faster than policy, review, or leadership awareness.
A practical example is easy to imagine. A legal or financial team uses an AI-enabled feature inside a familiar platform to summarize documents or draft communications. If no one has defined which files can be used, who can authorize that use, and how access is controlled, the business may create exposure without realizing it.
The old assumption was that unapproved data use happened only when staff broke the rules. Now it also happens when the rules never caught up to the workflow.
The fix isn't banning new technology by default. It's requiring governance before adoption. Classify the data first. Approve the use case second. Limit access throughout. That order matters.
How Technovation Builds Your Compliance Foundation
The biggest compliance gap in SMBs isn't lack of effort. It's lack of sustained operational control across messy environments.
Why local execution matters
A major blind spot is shadow data in multi-cloud environments. Only 39% of security engineers can track more than 75% of their company's sensitive data, according to multi-cloud data mapping findings. Manual tracking doesn't hold up when data spreads across file platforms, line-of-business apps, backups, user devices, and old repositories.
That problem hits DFW firms in practical ways. A clinic may have patient data copies in more places than leadership realizes. A law firm may carry years of matter-related documents across active, archived, and personal workspaces. A finance team may restrict production systems but overlook exported reports and duplicate spreadsheets.
What a practical partner actually does
In this context, a local operating partner brings substantial value. Technovation LLC helps businesses turn broad compliance goals into an actual control environment. That includes risk assessment, data visibility work, policy alignment, monitoring, remediation planning, and ongoing governance support tied to how the business functions day to day.
The firms that benefit most usually need help in a few specific areas:
- Finding what they have: Sensitive data inventories are often incomplete.
- Closing the gap between policy and enforcement: Written standards don't mean much if access and monitoring don't match.
- Building leadership accountability: Someone has to own priorities, timing, and evidence.
- Keeping pace with change: New software, remote staff, and client demands all require review.
For organizations that need strategic oversight instead of reactive support, a virtual CIO service for compliance and IT planning can help leadership connect risk decisions to budget, operations, and growth.
The right partner doesn't just hand over a checklist. The right partner helps the business build a system that survives audits, supports staff, and reduces avoidable exposure.
A DFW business that wants stronger data security and compliance doesn't need more generic advice. It needs a clear picture of current risk, a realistic roadmap, and help executing the work. Technovation LLC provides free security audits and IT health checks that help healthcare, legal, financial, construction, nonprofit, and general business teams identify gaps, prioritize action, and build a compliance foundation that holds.